What does strong enterprise cloud security entail, and how can you achieve it? With the prevalence of cyber threats and regulatory pressures, safeguarding your enterprise’s cloud infrastructure is more critical than ever. This article delivers direct insights on solid security frameworks, agile defensive tactics, and compliance adherence, providing the blueprint to reinforce your enterprise against the rigors of the cloud.
Key Takeaways
- Enterprise cloud security is vital due to increased cloud adoption and the significant financial and reputational risks associated with security breaches; a multilayered security strategy that includes encryption, access management, and compliance is essential.
- Challenges in cloud security, such as risks from multitenancy and cyber threats, require continuous monitoring and the implementation of robust controls like multi-factor authentication to prevent unauthorized access.
- ScaleGrid emphasizes a security-first approach, with comprehensive cloud security features for sensitive data protection, compliance adherence, and continuous improvement to protect against emerging cyber threats.
Cloud Security in Today’s Enterprise Landscape
The significance of cloud security has risen significantly in the current enterprise world. As more and more enterprises incorporate cloud-based systems, ensuring their security becomes a key concern. The fast pace at which these integrations are happening has brought about increased attention to potential risks associated with security breaches, along with specific obstacles that larger businesses encounter compared to smaller ones.
The Rise of Cloud Adoption in Enterprises
The adoption of cloud technology is leading to a shift in the business landscape. Enterprise organizations are turning towards enterprise cloud security solutions to make the most out of this transformation while minimizing potential risks. The selection process for a suitable cloud provider is crucial as it involves aligning business objectives, regulatory requirements, and current technological infrastructure with strong cloud security measures. An effective choice when securing their data on the cloud can greatly influence an organization’s success.
As more companies move away from traditional on-premises data centers, they enter into an era where scalability, flexibility, and cost-effectiveness become possible through various services offered by different providers in the market today. This presents enterprises with a wide range of options that cater specifically to their needs within this new framework created by multiple trusted cloud service providers.
The Consequences of Cloud Security Failures
Failure to properly secure the cloud can have devastating consequences for businesses. Neglecting compliance protocols may result in major financial and reputational harm. Companies have suffered losses of approximately $4.4 billion due to cyberattacks and data breaches, which include expenses like ransom payments, lost revenue, business disruptions, remediation costs, legal fees, and audit fees.
The impact of cloud security failures is evident from high-profile cases of data breaches that continue to cause damage by eroding customer trust and undermining a company’s credibility in the market.
Defining Enterprise Cloud Security
In today’s business landscape, the reliance on cloud services for data storage and processing has made enterprise cloud security a crucial factor. To ensure the protection of their sensitive data across public, private, and distributed clouds, large organizations implement various technologies, policies, procedures, and controls as part of their comprehensive approach to enterprise cloud security.
For effective safeguarding against potential threats and vulnerabilities in this digital age, it is recommended that enterprises adopt a multilayered security strategy coupled with implementing Zero Trust principles. This proactive approach also needs to take into consideration complexities arising from multi-cloud or hybrid cloud strategies to achieve holistic enterprise cloud security.
The Anatomy of Enterprise Cloud Security
To effectively secure an enterprise cloud, one must have a thorough understanding of its complex structure. A protected cloud environment is built upon multiple layers that include data encryption, access management, and compliance measures. Data encryption acts as a strong barrier by making sensitive information unreadable to unauthorized parties in order to ensure the security of data.
On the other hand, access management establishes necessary mechanisms and policies for controlling access to cloud resources so that only authorized users can obtain sensitive information. Governance and compliance are also crucial factors in ensuring enterprise cloud security as they enforce regulatory requirements and best practices within organizations.
Tackling the Challenges of Cloud Security
Enterprises face a unique array of challenges related to cloud security. The distinct security challenges that cloud environments encounter include:
- Risks associated with multitenancy
- Cyber threats like malware and misconfigured storage
- Unauthorized data access
- A range of cyber threats, including file upload attacks
These challenges demand the utilization of suitable security tools, revising security policies, and ensuring continuous security training and a security-focused organizational culture.
Read also: AI in Cloud Computing
Identifying and Overcoming Cloud Security Threats
Ensuring the security of private cloud environments is crucial for any enterprise. The ever-growing list of potential threats to cloud security includes misconfiguration, unauthorized access, insecure interfaces, account hijacking, data breaches, malware attacks such as phishing and denial-of-service (DoS) or distributed denial-of-service (DDoS), as well as SQL injections.
To effectively protect against these risks in their use of cloud resources, enterprises can rely on specialized tools. These assist with identifying vulnerabilities through conducting thorough assessments and scanning activities specifically designed for evaluating configurations related to storage and overall vulnerability within the company’s chosen cloud service provider(s).
Read also – Key Advantages of DBMS for Efficient Data Management
Strategies to Prevent Unauthorized Data Access
Enterprise cloud security is significantly threatened by unauthorized data access. Implementing strong security controls is essential for preventing unauthorized data access in enterprise cloud security. These controls are further bolstered by multi-factor authentication, which mandates the use of multiple forms of verification, providing an additional layer of protection.
Continuous monitoring plays a crucial role in preventing unauthorized data access by:
- Actively tracking and analyzing cloud infrastructure in real-time to prevent unauthorized access
- Promptly identifying and addressing security incidents
- Maintaining compliance through regular updates and user training.
Core Components of a Secure Cloud Strategy
A solid cloud security plan should include two critical components: access management and data encryption. By encrypting sensitive information, the risk of a breach is minimized as it can only be accessed with an encryption key, even if unauthorized users obtain access to it.
Access management plays a crucial role in regulating resource accessibility by establishing rules for who has permission to view or use certain resources under specific conditions. This ensures that confidential data remains protected from unauthorized individuals accessing it.
Data Encryption: The Shield for Sensitive Information
Data encryption is a crucial aspect of an effective enterprise cloud strategy, particularly when dealing with confidential information. This process involves converting regular data into a coded form, which helps to protect its privacy and guard against cyber threats.
By utilizing data encryption techniques, sensitive information remains inaccessible even if it is compromised by unauthorized parties. The use of corresponding keys ensures that only authorized personnel can access the encrypted data, making it an essential element in ensuring robust security for enterprise clouds.
Access Management: The Gatekeeper of Cloud Resources
An important element of ensuring a secure cloud strategy is access management. This technique verifies user identities and controls their permissions within the cloud environment. Access management improves overall security by enforcing strict access policies, managing user privileges to resources, and monitoring cloud identities to prevent unnecessary entitlements.
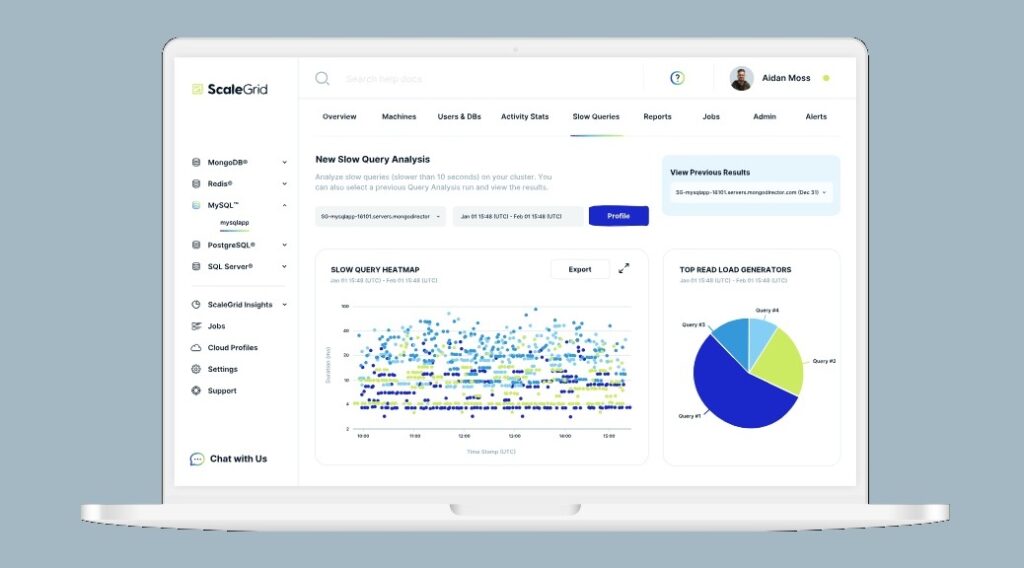
ScaleGrid’s Mission for Secure Cloud Environments
ScaleGrid has a strong focus on providing secure cloud environments. Its key emphasis is on data security and ensuring compliance, while still allowing users to maintain control over their database systems and data, even when they are hosted in the public cloud.
Security-First Approach
ScaleGrid prioritizes security by incorporating it into its overall strategy. Through automation, their approach provides continuous monitoring and enhanced protection for enterprises using their DBaaS platform. ScaleGrid also offers comprehensive features and support to Strengthen the security of its services.
Commitment to Continuous Security Improvement
At ScaleGrid, there is a strong dedication to continuously enhancing security protocols and proactively safeguarding installations against potential threats. The company takes necessary measures to ensure suitable levels of protection are in place for their systems at all times. Proactive efforts are consistently taken to maintain the ongoing security of these systems.
ScaleGrid’s Cloud Security Solution
At ScaleGrid, we prioritize the security of our customers’ data and applications. We offer a range of robust cloud security features such as encryption to protect sensitive information from potential threats. Our commitment also extends to ensuring compliance with industry standards for safeguarding user personal information. With various carefully implemented measures in place, our platform provides comprehensive protection against unauthorized access to customer data.
ScaleGrid’s Data Security Measures
ScaleGrid employs a range of measures to safeguard customer data. These include activating SSL encryption on MongoDB® servers and utilizing Cloud Profiles that come with specific configurations for security groups and subnets, ensuring secure storage practices.
Compliance and Governance: ScaleGrid’s Assurance
ScaleGrid guarantees adherence to industry regulations and governance standards to protect User Personal Information from unauthorized access. We have implemented appropriate measures and protocols to monitor costs, operations, security compliance, data management, performance tracking, and the configurations of all cloud resources.
Best Practices for Improving Cloud Security
Incorporating cloud security best practices is a crucial step in enhancing the overall security of enterprise cloud environments. These measures involve enforcing strong and reliable security protocols, as well as conducting frequent evaluations to ensure optimum protection against potential threats. Choosing the right enterprise cloud security solution starts with examining the cloud service providers that align with your business goals, compliance needs, and current tech stack.
Implementing Robust Security Protocols
Ensuring a secure cloud environment requires the implementation of strong security protocols, including SSL/TLS, SSH, IPSec, identity and access management (IAM), and multi-factor authentication (MFA). It is also crucial to follow the principle of least privilege and regularly conduct audits. Data encryption should be applied along with robust access controls and efficient encryption key management procedures.
Regular Security Assessments and Event Management
To effectively mitigate potential vulnerabilities in a cloud setup, it is crucial to conduct regular security assessments and employ event management techniques. These measures involve thoroughly evaluating the overall security status of a cloud computing system by identifying any weaknesses in its configuration, potential threats, and existing vulnerabilities.
Event management is essential in detecting targeted attacks or data breaches within organizations, especially through Security Information and Event Management (SIEM) tools. By closely monitoring events occurring within the cloud, SIEM helps identify malicious activities that may result in compromised data integrity.
Aligning Best Practices with ScaleGrid Solutions
ScaleGrid’s solutions are designed to comply with top industry standards for cloud security by incorporating enhanced security measures. They seamlessly integrate with popular databases including MongoDB®, Redis, MySQL, and PostgreSQL while utilizing their respective built-in security frameworks. This ensures the highest level of protection for data stored in these databases on the cloud.
By implementing advanced levels of security protocols and working closely with recognized database providers such as MongoDB®, Redis, MySQL, and PostgreSQL. ScaleGrid provides adherence to best practices for safeguarding against potential threats.
How ScaleGrid Integrates with Security Frameworks
To offer a complete security solution, ScaleGrid works seamlessly with various security frameworks. This integration greatly strengthens cloud security and ensures compliance by enhancing data integrity and consistency, as well as facilitating efficient access and sharing of information.
Case Studies: Enhanced Security with ScaleGrid
Examples and real-world scenarios showcase the effectiveness of ScaleGrid’s offerings in enhancing security for enterprise cloud environments. A case in point is OpenAQ, which successfully deployed a robust PostgreSQL solution through ScaleGrid’s ‘Bring Your Own Cloud’ feature on AWS. This enabled them to effectively manage and safeguard their air quality data.
Preparing for Tomorrow: ScaleGrid and Future Cloud Security Trends
ScaleGrid is well-prepared to address upcoming cloud security challenges. We understand the importance of anticipating changing security threats and take action by:
- Protecting user personal data from unauthorized access
- Securing deployments using Security Groups and customized firewall rules
- Complying with industry standards for maintaining data security.
Anticipating Evolving Cyber Threats
Staying up-to-date with emerging threats is a top priority for ScaleGrid in ensuring the success of its solutions. One notable trend seen lately is an increase in cloud-based attacks, accounting for 20% of all cyber attacks in 2020.
In light of these evolving dangers, ScaleGrid has taken proactive measures to fortify installations and prepare our infrastructure against potential risks targeting cloud environments. These measures are constantly being reviewed and updated to stay ahead of any new or current cloud security threats that may arise.
Staying Ahead in the Cloud Migration Journey
ScaleGrid offers reliable and adaptable solutions to assist businesses in staying ahead in their journey of transitioning to the cloud. We prioritize security during this process by employing data encryption measures, as well as utilizing Cloud Profiles that encompass all necessary settings for the particular cloud being utilized, including aspects like security groups and subnets.
For rapidly growing enterprises, ScaleGrid’s ability to dynamically scale is crucial in efficiently managing hosting deployments within the cloud environment. This allows us to effectively cater to the evolving needs of expanding organizations during their transition phase into using cloud technology.
Summary
Enterprise cloud security is an essential factor in today’s business operations. ScaleGrid understands this and strives to provide secure cloud environments while continuously enhancing security protocols. As a trusted partner on your journey into the cloud, we offer integration with top-notch security frameworks, robust features for securing the cloud, and adherence to best practices. With constant advancements in security threats and changes within the world of clouds, ScaleGrid remains prepared to help enterprises stay ahead during their migration process.
Visitors also read:
- DBaaS vs Self-Managed Cloud Databases
- Mastering Distributed SQL Databases in 2024
- One Cloud Doesn’t Fit All Anymore
- 6 Major DBaaS Challenges for Modern Enterprises
Frequently Asked Questions
What is enterprise cloud security?
Enterprise cloud security refers to the measures implemented by large companies for safeguarding their digital assets, such as data and IT infrastructure hosted on public, private, or distributed clouds. This involves utilizing technologies, policies, and controls to ensure the protection of sensitive information in these environments.
What are the four areas of cloud security?
The four fundamental aspects of maintaining a secure cloud environment include having visibility into and control over data, managing access to both the data and applications within the cloud, as well as ensuring compliance with relevant regulations. These pillars are essential for safeguarding against potential threats in a cloud security setting.
What is the significance of security in a cloud environment?
Cloud security is crucial in today’s enterprise landscape due to the growing integration of cloud-based environments, which brings a heightened awareness of the potential repercussions of security breaches and the unique challenges faced by enterprises in contrast to midmarket businesses.
How does ScaleGrid ensure the security of its cloud environments?
At ScaleGrid, the protection and safety of our cloud environments are top priorities. We maintain strict security measures including Security Groups, customized firewall rules, and adherence to industry standards for data security to prevent unauthorized access to personal information belonging to our users.