What does it take to secure your cloud assets effectively? Cloud security monitoring is key—identifying threats in real time and mitigating risks before they escalate. This article strips away the complexities, walking you through best practices, top tools, and strategies you’ll need for a well-defended cloud infrastructure. Get ready for actionable insights that balance technical depth with practical advice.
Key Takeaways
- Cloud security monitoring is a comprehensive approach involving both manual and automated processes to oversee servers, applications, platforms, and websites, using tools that are customized to fit unique cloud architectures.
- Continuous cloud monitoring enables real-time detection and response to incidents, with best practices highlighting the importance of assessing cloud service providers, adopting layered security, and leveraging automation for efficient scanning and monitoring.
- Advanced cloud security monitoring tools, like Exabeam Fusion SIEM and Sumo Logic, provide extensive analysis, integrate with existing infrastructure, and aid organizations in responding to threats while maintaining regulatory compliance and managing potential challenges in integration and functionality.
The Importance of Cloud Security Monitoring
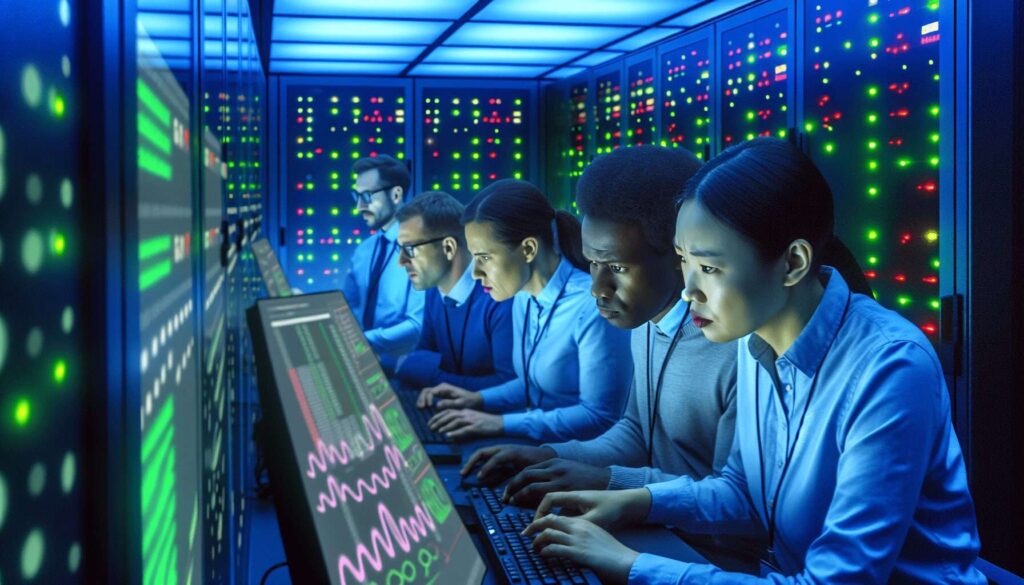
Cloud security monitoring goes beyond simply observing digital assets, using a comprehensive approach that combines manual and automated processes to assess the security of cloud environments. This includes servers, applications, software platforms, and websites.
Customized security measures tailored to the specific architecture and workloads of each organization’s cloud infrastructure can effectively protect data from potential threats or vulnerabilities.
One major advantage of this method is automation, which enables more efficient measurement and evaluation of behaviors related to data usage, application functionality, and overall infrastructure health. The automatic nature also allows for quick response times in addressing any identified security concerns making it an ideal solution for effective cloud security monitoring.
Continuous Monitoring in Cloud Environments
A key element of the cloud security strategy is cloud monitoring, which plays a crucial role in continuous security monitoring, real-time detection, and response to security incidents, thereby ensuring the safety and integrity of data and applications. The importance of security monitoring work in the context of cloud security monitoring work cannot be overstated, as it is vital for maintaining a secure environment.
To make efficient use of time and resources, best practices suggest assessing cloud service providers, adopting a layered approach to cloud security, and leveraging automation for scanning and monitoring. Real-time assessment and scanning offer the benefit of enabling organizations to anticipate a prompt and timely threat response process, ensuring rapid detection and mitigation of issues as they arise.
Read also – Enterprise Cloud Security Strategy For 2024
Cloud Security Monitoring Tools and Techniques
When it comes to monitoring cloud security, we have a wide range of tools and techniques available. These include options offered directly by the cloud service providers themselves as well as solutions from third-party companies that specialize in security services. On-premise management tools can also be integrated with the cloud for enhanced protection.
Sophisticated monitoring solutions like Exabeam Fusion SIEM and Fusion XDR provide thorough analysis, behavioral analytics, and automated features to improve the identification of advanced attacks and insider threats. By enhancing IAM (Identity Access Management), CASB (Cloud Access Security Broker), and SASE (Secure Access Service Edge) capabilities, these technologies bolster overall cloud security measures.
One effective option is Sumo Logic’s platform, which seamlessly integrates into existing infrastructure for both on-premises environments and the public or private clouds being used by an organization. Through this integration process,integrated teams are better able to investigate potential risks and prioritize actions based upon insights gained through log data collected through their chosen Cloud Monitoring Solution.
This way, relevant information can easily be accessed, allowing swift responses against possible external attacks or internal threats. On account of utilizing top-of-the-line technology, data collection, and reporting mean real-time deployment, keeping security management up-to-date, and in tune with current digital standards while staying ahead against emerging risks from cybercrime services along with data breaches perpetuated through computing platforms, ensuring cloud users that any accessible sensitive files remain safe.
Strategic intervention, about personally identifiable information, is another beneficial key application path included within said mitigation strategy that requires extra support ever demanded, necessitating more focused ground-up protection strategies at times when personal confidentiality isn’t ensured.A. A. A.
Native and Third-Party Solutions
Both native and third-party options offer unique advantages when it comes to monitoring cloud security. Native tools, such as CloudWatch from AWS, have more extensive integrations and provide comprehensive protection for data in the cloud compared to their third-party counterparts. Of course, this is only true if the native solutions are used within the corresponding environment.
There is a wide selection of advanced solutions available for cloud monitoring, including various choices for ensuring top-notch security in your organization’s systems. For example, Blumira offers a third-party solution while AWS provides its own with CloudWatch. Depending on specific requirements or preferences, an organization may have these solutions that can either replace existing tools or be integrated into current infrastructure to enhance capabilities related to managing security concerns in a multi-faceted manner across different areas like data management and overall system stability within relevant environments.
Integration with Existing Security Management Tools
Integrating cloud security monitoring with established security management tools offers several benefits, such as ensuring compliance with regulations, tracking and evaluating the security of servers and applications, taking control of existing security systems, managing access points effectively, and receiving alerts for suspicious activity.
Nevertheless, this integration can present certain challenges to organizations. These include dealing with a multitude of available security tools, maintaining interoperability between different systems, lack or compromise in functionality when merging multiple solutions, integration complexity, difficulties in maintaining visibility and control, cost constraints, vendor compatibility issues, network integration concerns, and securing APIs.
Addressing Challenges in Cloud Security Monitoring
While cloud security monitoring offers numerous advantages, it also presents a few challenges that must be addressed. These include alert fatigue, lack of context, and absence of strategy. To effectively overcome these obstacles, understanding their nature is crucial, and implementing appropriate solutions is essential.
Alert fatigue refers to the overwhelming number of cybersecurity alerts which can impede the ability to respond promptly and accurately to legitimate threats. To combat this issue, certain strategies are recommended such as prioritizing alerts based on severity levels, reducing false positives through advanced detection techniques, automating response protocols for faster action-taking, and providing adequate training and resources for personnel responsible for managing security.
Although cloud security monitoring has its own set of difficulties like excessive alerts or inadequate contextual information, by addressing issues such as alert overload with effective measures like categorization according to importance level, troubleshooting potential inaccuracies in threat reports via sophisticated methods, and streamlining reaction procedures using technology while consistently investing in developing human capabilities, a secure digital environment can still be maintained within organizations leveraging cloud technologies efficiently against diverse dangers without losing sight on overarching defensive plans overall.
Cloud Security Monitoring Solutions
Effective monitoring of cloud security requires the implementation of robust strategies. These strategies should guarantee compliance with regulations and include endpoint security solutions. Adhering to standards such as ISO 27001, ISO 27017, PCI DSS, and HIPAA is essential in ensuring that an organization’s infrastructure and services meet defined security requirements and comply with applicable laws.
Endpoint security solutions play a crucial role in enhancing cloud security monitoring by providing advanced threat intelligence capabilities for promptly detecting threats on cloud-based endpoints. They also aid organizations in maintaining compliance and governance.
Apart from implementing compliance measures and endpoint security solutions, a mature information security solution is needed.
Compliance and Regulation
Ensuring compliance with security regulations is crucial when it comes to monitoring cloud security. It is essential to guarantee that the utilization of cloud services adheres to established security and compliance standards, as well as relevant laws and industry norms.
Non-compliance can result in severe consequences for organizations. Those who fail to comply with regulation may face hefty fines up to $500,000 along with losing their merchant accounts and suffering damages in case of a data breach. In some instances, companies have been subjected not only to significant penalties but also to legal action for non-compliance regarding data breaches and privacy violations.
Endpoint Security Solutions
Endpoint security is an essential aspect of protecting cloud environments and involves a range of practices and technologies to safeguard endpoint devices and enhance overall network security. These solutions, including CrowdStrike, Bitdefender, Eset, Kaspersky, and McAfee, employ threat intelligence capabilities to quickly detect and prevent threats in cloud-based endpoints. Endpoint security plays a crucial role alongside other techniques such as network security tools for comprehensive cloud monitoring.
Leading endpoint security solutions are vital components in the protection of the rapidly growing use of technology across various industries today where there exists great dependence on securing endpoints.
Real-World Examples of Cloud Security Monitoring Success
The practical application of cloud security monitoring goes beyond just theoretical ideas. There are numerous real-life instances where businesses have effectively utilized this approach to safeguard their data and prevent cyber attacks. Notable examples include the use of tools such as Wiz, Microsoft Defender for Cloud, Lacework, IBM Security QRadar SIEM, and CrowdStrike Falcon Cloud. Companies like Palo Alto Networks Cloud Security, Fortinet Cloud, and Trend Micro.
Future Trends in Cloud Security Monitoring
The realm of cloud security monitoring is constantly changing. As technology advances, so do the trends and techniques in this field. A major trend is the growing use of hybrid and multi-cloud environments, which poses unique challenges for securing data at connection points as well as across multiple clouds.
In upcoming developments, we can anticipate a greater reliance on artificial intelligence (AI) and machine learning for effective cloud security monitoring. These innovative tools have the potential to detect irregularities in data transfers, prevent breaches, and improve accuracy when identifying threats.
Edge computing will play a critical role in enhancing overall security by minimizing the transmission of sensitive information over long distances while also presenting new obstacles with regard to protecting expanded perimeters.
ScaleGrid’s Role in Improving Cloud Security
The security of cloud systems is greatly enhanced by ScaleGrid, thanks to our comprehensive range of monitoring tools specifically designed for this purpose. These include real-time alerting features and a specialized dashboard that provides crucial database and OS metrics. Proactive monitoring capabilities are also available, along with detailed reports on databases and clusters.
With these powerful tools at their disposal, organizations can effectively safeguard their data and infrastructure from potential threats or vulnerabilities. To bolster protection measures, ScaleGrid follows a proactive approach towards ensuring security, which includes robust features for sensitive data protection as well as compliance adherence. This has yielded positive results for many businesses using ScaleGrid’s services, as seen through our success stories.
Summary
Cloud security monitoring is becoming increasingly important in today’s fast-paced digital world. Organizations must use a combination of manual and automated methods to safeguard their data and infrastructure against potential risks. With continuous monitoring, real-time evaluations, and the implementation of strong security techniques and tools, organizations can ensure the protection and integrity of their data and applications.
In the future, advancements in AI/ML technology along with a more widespread adoption of multi-cloud/hybrid cloud environments will have a significant impact on how we approach cloud security monitoring. ScaleGrid offers a comprehensive range of top-notch security monitoring solutions alongside its prioritization for ensuring optimal levels of safety for an organization’s digital assets during this ever-changing landscape.
Further reading:
- DBaaS vs Self-Managed Cloud Databases
- Mastering Distributed SQL Databases in 2024
- One Cloud Doesn’t Fit All Anymore
- 6 Major DBaaS Challenges for Modern Enterprises
Frequently Asked Questions
What is cloud security monitoring?
The practice of cloud security monitoring entails the examination, supervision, and observation of operational procedures within a cloud setting. This process employs both manual and automated methods to monitor and evaluate security measures in place for safeguarding the integrity of data within the environment. Overall, it is focused on ensuring heightened levels of security.
What are the 4 areas of cloud security?
Cloud security is comprised of four main areas: visibility into cloud data, control over this data, access to both the data and applications in the cloud environment, as well as ensuring compliance with regulations. These aspects are essential for maintaining a secure and protected atmosphere within the cloud. The protection measures involve different aspects related to safeguarding data and applications stored on or accessed through the cloud platform.
What is cloud-based monitoring?
Monitoring cloud-based resources involves the assessment and control of various components to guarantee efficient functioning and prompt resolution of any potential disruptions that could impact users. This encompasses constant evaluation and management of different elements within the cloud infrastructure to maintain a high level of availability, as well as performance.
What is the most effective cloud security?
To ensure optimal cloud security, it is essential to utilize advanced intrusion detection and prevention technology, adhere to compliance regulations through thorough checks, explore potential cloud security solutions, and conduct regular audits of the system’s integrity. Additionally, it is important to activate and monitor all security logs.
An additional measure that must not be overlooked for safeguarding sensitive data during transmission is implementing end-to-end encryption methods. By doing so, the information will remain secure at all times throughout its journey in the cloud network.
What are some examples of cloud security monitoring tools and techniques?
The safeguarding of cloud services can be bolstered through a range of monitoring tools and techniques, including those offered directly by cloud service providers, third-party options, as well as on-premise security management solutions. To these traditional measures, advanced software like Exabeam Fusion SIEM and Fusion XDR are also available for enhanced protection.
These various tools can significantly strengthen security protocols in a cloud environment. By incorporating them into your current system, you can effectively monitor and manage potential threats to maintain the safety of your valuable data stored within the cloud.